
Wain briefly lived in a care facility in northern Tasmania before being sent to Japan.
Read More
Drinking coffee can still be done by those with stomach problems.
Read More
These Moroccan beauty tips will leave you feeling rejuvenated from head to toe.
Read More
The popularity of these animals has led the zoo to be criticized.
Read More
She likes to do a beer shower whenever she finishes filming or a reasonably strenuous activity.
Read More
These clean and hilarious jokes for adult will surely tickle your funny bones and make you laugh out loud.
Read More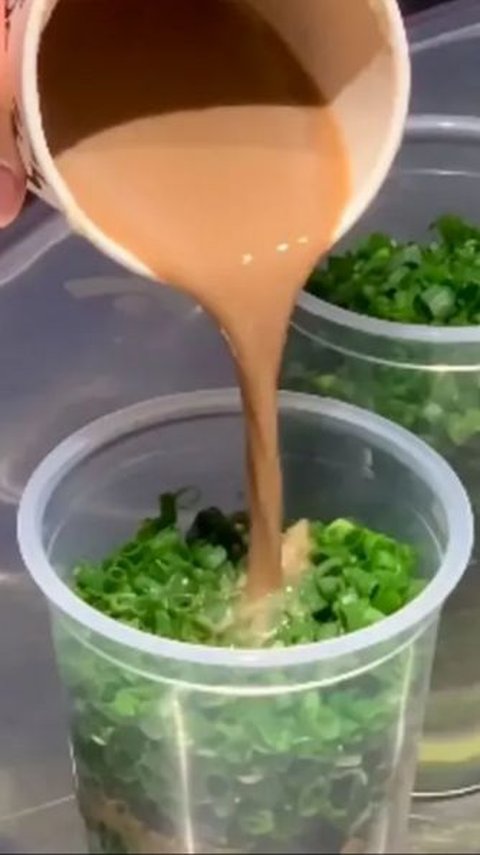
People wondered if the presence of the ingredient would spoil the coffee's flavor.
Read More
Unpredictable weather causes us to often experience a cold, especially at night.
Read More
The emergence of hunger in the middle of the night can be very disturbing and can be avoided in various ways.
Read More
These sites will give you a chill as you explore the paranormal past of this historic city.
Read More
These calming words will touch your heart with serenity and refresh your mind with clarity.
Read More
After about 14 hours, their efforts were declared successful.
Read More
Here are some of the best and most realistic sim racing games that every racing fans should play.
Read More
India is taking a step forward in improving its Navy's anti-submarine warfare capabilities.
Read More
These Dune quotes from the movie capture the essence of Herbert's masterpiece.
Read More
The caffeine content in coffee, tea, and chocolate varies and has different effects.
Read More
Here are five ASMR sounds that can help relieve anxiety or a panic attack.
Read More
According to researchers from Harvard, here are ways to help children learn from their mistakes.
Read More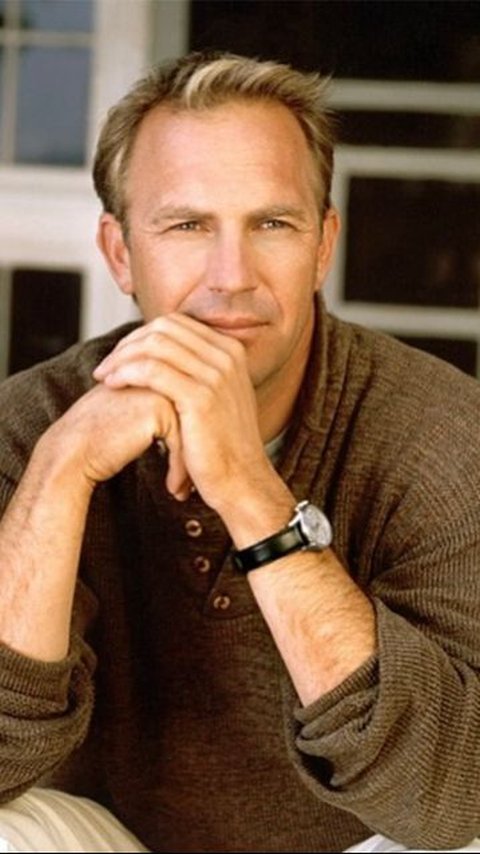
Kevin Costner is known for his charismatic on-screen presence and versatile acting abilities. Here is our pick of the best Kevin Costner movies you should watch
Read More
Food poisoning needs to be handled quickly and correctly.
Read More
The right hobbies can be a way for the elderly to maintain their health and fitness properly.
Read More
These Bane quotes encapsulate his philosophy, cunning, and sheer force of will.
Read More
Children's learning styles greatly determine how they can absorb information to the maximum.
Read More
Here are five of the most iconic and beautiful Hollywood actresses of the 2010s!
Read More
From the beautiful Davao City in the Philippines to the mesmerizing Ninh Binh in Vietnam, here are the best underrated destinations in Southeast Asia for you.
Read More