
These haunted places in Chicago will leave you with a spine-tingling experience.
Read More
Korean actors and actresses have gained recognition in Hollywood and show their talent and versatility on the international stage.
Read More
These are the greatest Nicolas Cage movies you should watch that show his versatility and his ability to bring a character into life.
Read More
The hot weather lately has made it difficult for us to sleep well at night.
Read More
Each killer robot movie on this list has a unique take on the action genre, from classic action-packed thrills to thought-provoking of robots.
Read More
The routines and exercise patterns we do every day can help build muscles.
Read More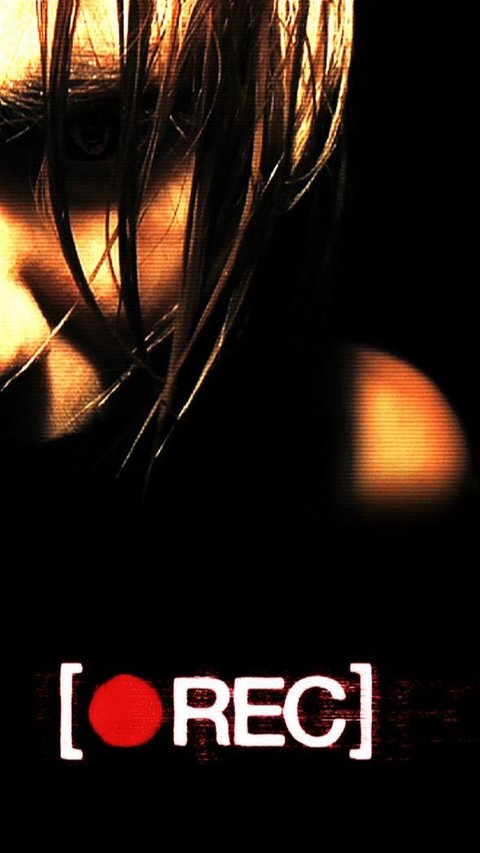
First-person point of view restricts what the audience sees to the viewpoint of a single character.
Read More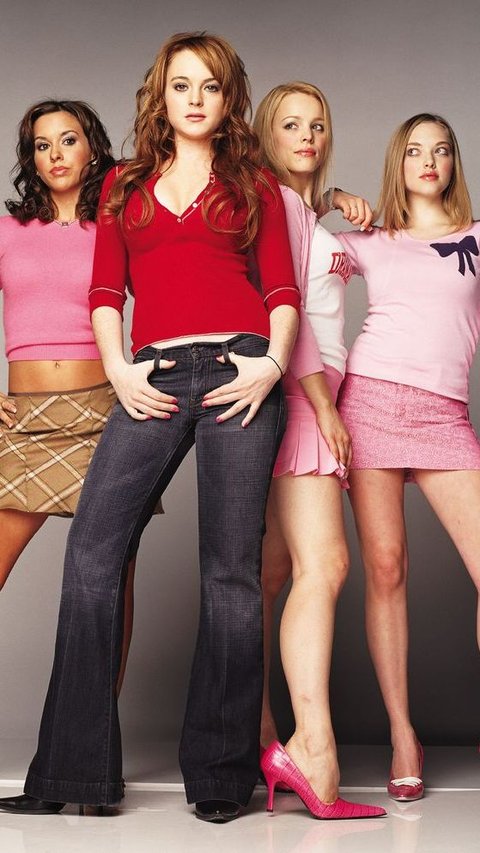
The popularity of these Mean Girls Quotes makes this movie legendary.
Read More
If you are going to visit Rotterdam for the first time, here are some of the best places to visit in Rotterdam you must put in your itinerary.
Read More
Consuming apple cider vinegar before bed can provide several health benefits for the body.
Read More
Here are five video games that feature elements of feudal Japan you must play!
Read More
The chocolate mousse recipe is a classic, silky smooth dessert from France that are loved by many chocolate fans around the world.
Read More
To accelerate the growth of children's height, several sports can be done.
Read More
Knowing what to eat before workout and when to eat it is important. The food you eat give you the energy for your workout and make it more effective.
Read More
These my son quotes contain wisdom, strength, and resilience that can inspire our sons.
Read More
He died in Surrey last Saturday after doctors were unable to help repair his organs.
Read More
Taylor Swift knows how to shake it off with humor.
Read More
ByteDance has 270 days to get rid of its stake in TikTok, but this lawsuit might delay that.
Read More
Do you love fishing? If so, these fishing quotes will remind you the joys you feel when you are fishing.
Read More
Jimmy Donaldson, a.k.a MrBeast recently turned 26 years old this year and will shows both his generousity and climate crisis awareness.
Read More
Through selfish parents quotes, we can explore the impact of selfish parenting.
Read More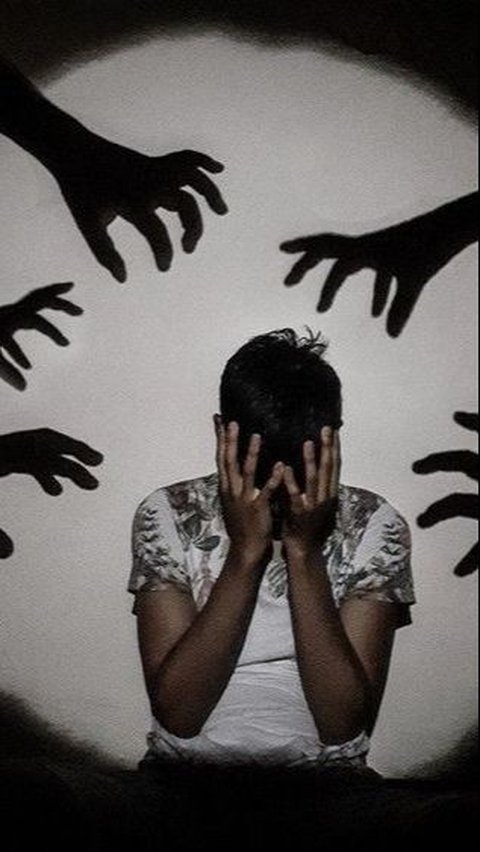
These manipulation quotes will help you to understand more about manipulation so you can be free from a toxic relationship.
Read More
Here is the complete list of winners of the 60th Baeksang Arts Awards 2024.
Read More
Northumberland has a wide range of attractions that invite all interests and preferences.
Read More
These phrases express a parent's depth of love and admiration for their daughter.
Read More