
Pain and discomfort in the feet may arise when standing all day. Follow these methods to overcome it.
Read More
Increasing fetal weight can be done by consuming a number of healthy foods as follows.
Read More
AI ethicists argue that digital recreations of the dead are in dire need of regulation.
Read More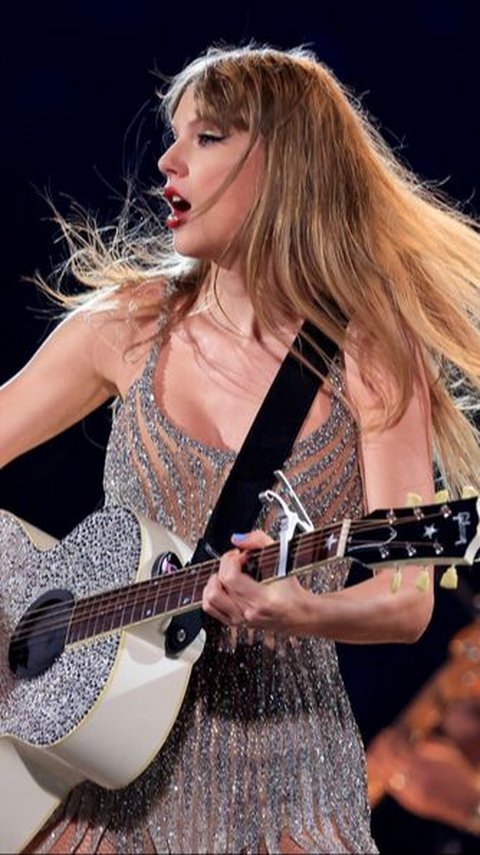
Taylor Swift fans know how to rock a stadium with "Shake It Off".
Read More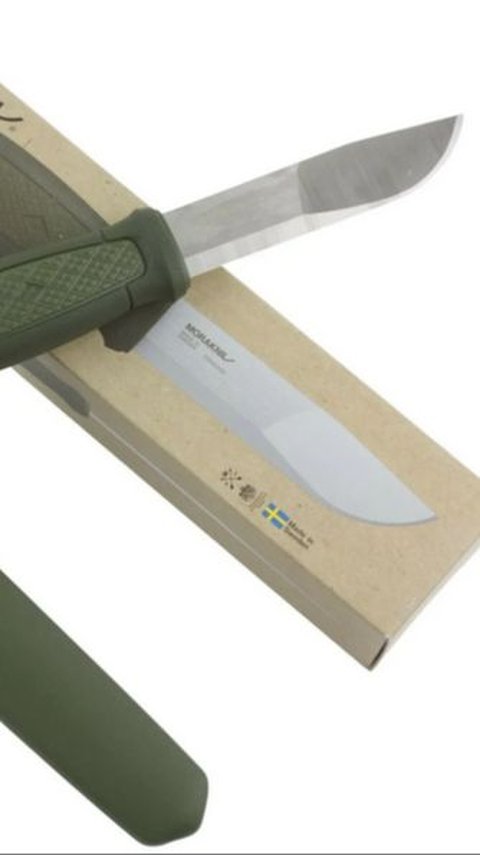
This collaboration results in a durable, high-quality knife.
Read More
These funny Euphoria quotes capture some of the most hilarious moments in the series.
Read More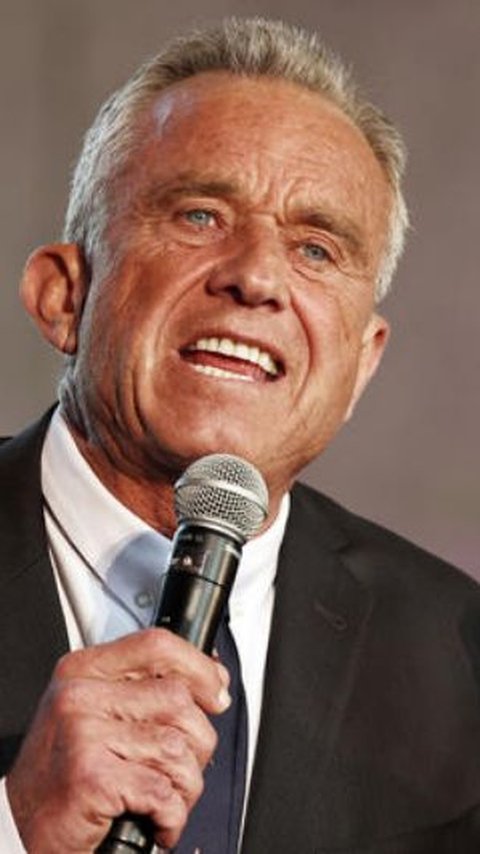
Robert F Kennedy (RFK) Jr. once thought he had a brain tumor.
Read More
Explore the legends and lore of these sites, but be prepared for a scary experience you will remember.
Read More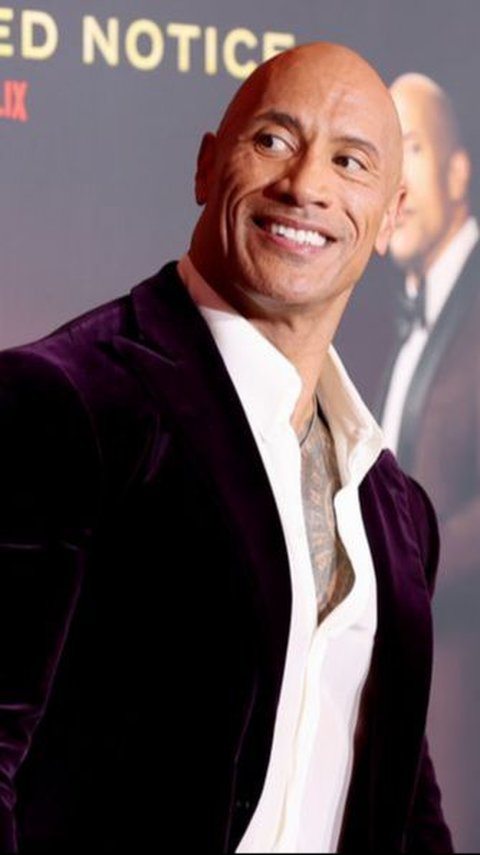
From Dwayne "The Rock" Johnson to Dainel Craig, here are 10 celebrities who are secretly gamers.
Read More
A Bring Me The Horizon fan was trolled on a Reddit forum for thinking that the band was Christian.
Read More
Justin Bieber announced that his wife, Hailey Baldwin, is pregnant with their first child.
Read More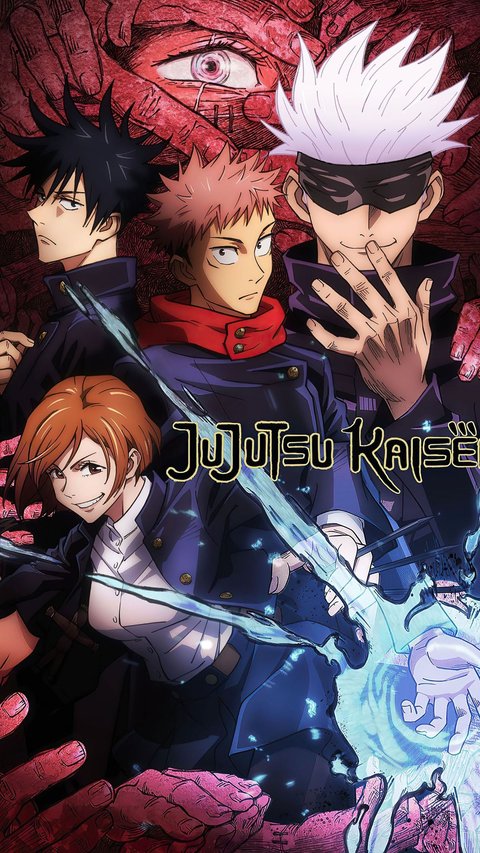
Here are 6 anime you should watch if you like Jujutsu Kaisen.
Read More
Incorporating these ancient Roman beauty hacks into your routine can help you achieve a flawless and radiant look.
Read More
Keloids can form due to improper and incomplete wound healing.
Read More
"Isekai" is a popular subgenre in anime where characters are transported to or reincarnated in a parallel world.
Read More
From the breathtaking Lake Tahoe to the lively city of Chicago, here are the best places to visit in June in the USA.
Read More
In early age, babies have stages of language development as they grow older.
Read More
Here are 5 unique facts about apple you probably never heard about!
Read More
The fondue recipe originated from Switzerland. This is a perfect dish for any cheese lover out there.
Read More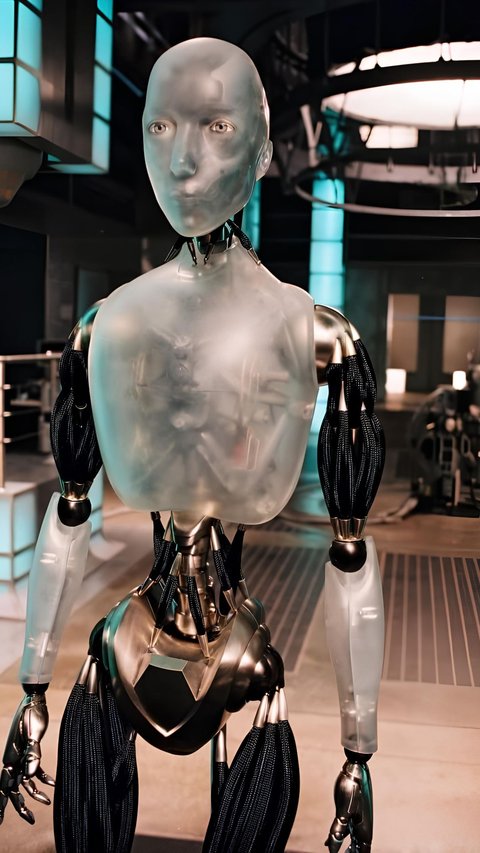
Each movie about AI has a unique perspective on the potential dangers and dilemmas of rising AI technology.
Read More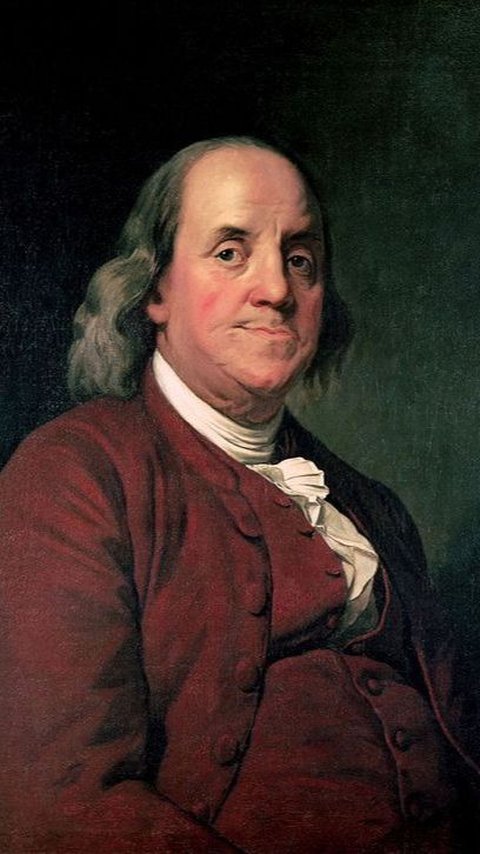
Learn more about liberty, life, and success from these Ben Franklin quotes.
Read More
This article talks about what is accounting and the functions of accounting to help you understand why it is a key aspect in a successful business.
Read More
EA Games may use AI tools for video game development soon enough.
Read More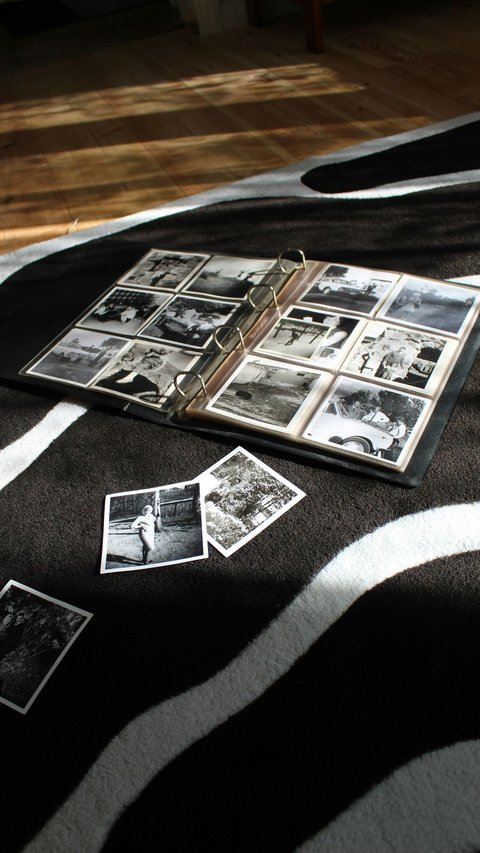
These beautiful quotes about memories will remind you every priceless, and happy memories with your loved ones.
Read More
It will raise the competition with the most known search engine, Google.
Read More